And does this require an Internet firewall which allows a certain sort of traffic (without configuration)? I know that my Netgear router doesn't pass-through VPN traffic, for example. Or was it necessary to configure something like a port forward on the router?
All you need to to allow is ssh through the firewall. So if you already have ssh enable you don't need to do add anything else. It will be handled directly via putty and ssh. When you configure putty you will configure the putty session with the destination port and ip adress for the local port. So say you configure local port 8080.
It looks like this in putty under ssh/tunnels L8080 192.168.100.149:80
Which means when you connect to local 127.0.0.1:8080 Putty will then forward that via the ssh connection that is actively connected to your home server to ip 192.168.100.149 port 80. The ip is the octoprint server on your local network at home. This all goes over ssh and is not in the clear. No DNS entries are needed as it is going from ip to ip directly over ssh via the connected ssh session already established.
Jim
@Jimbrown719 I'll spend some time to add some graphics to all this so that people will better understand what's going on. I'm reading from here, btw.
- This approach usually relies upon a known external (static) IP address so that the internal box ("my main home server") can initiate an outbound tunnel via
ssh. People typically have a Linode or similar resource for this. (Many of the remote-my-PC softwares have your PC initiate a connection to their server, which then is the cloud-based connection point for the client side of their solution.) - Since 8080 is above 1024, less restrictions are given to it from the router's or the computer's standpoint.
To me, this sounds a little fishy. The safe solution involves your home computer initiating the session outbound. Anything where an inbound connection is initiated implies to me some sort of router-forwarding.
Let's say that I'm at Starbuck's and I want to connect to my own local server. If I try to simply ssh back to the private IP address of my local server, that won't route and fails. Any inbound attempt needs to know my router's public IP address. *
Reversing this, I note my Starbuck's-issued IP address and leave my laptop there. I go home and initiate an outbound connection to the laptop. Assuming that Starbuck's router is okay with this, I now have the tunnel active. I assume that I return to Starbuck's and can see my server at home.
* I could manually add a route on my laptop which directs traffic to that private IP address range at home to go through my router's public IP address, assuming that the router will forward it.
You start off with a good document but you lost me at everything after you say my ssh connection sounds fishy?. You never have to have a route on your laptop at star bucks to the home server running sshd. Everything is statically setup within the tunnel no routes are needed. The port you setup never gets used outside of the laptop when you hit the port the tunnel is using it gets sent out the ssh connection on port 22. SO if someone was watching the traffic leaving your laptop all that would be seen is secure ssh traffic going out port 22.
The referenced document appears to include an extra entity, a server in the cloud which assists in all this.
In your case, I'm not seeing the extra server with a public IP address. Perhaps I don't understand the layout of what you have.
I've been an I.T. Manager for a very long time, btw.
Here are the players which I see:
- A) Your internal OctoPrint Web Server with a private IP address
- B) Your internal main home server with a private IP address
- C) Your Internet firewall
- D) Your sometimes-external Windows laptop
D -> B over ssh ("I create an ssh session to my main home server"). The laptop then sees it's own http://localhost:8080/ as forwarded over to http://A-Internal-IP-Address:80/
Underlying all this is that your laptop needs to route packets from outside your home into your home. That's the part that has me scratching my head. In the linked version, that B entity is in the cloud and yours is there inside your private network. Perhaps I'm not following the nuances of your setup.
I currently get "Possible external access detected" with 1.3.10rc2 even though I have no forwarding or anything else related to trying to get external access.
I also have another Octoprint printer running but it doesn't give this warning.
How exactly does Octoprint determine we are trying to expose externally? Just curious so I can check the instance to see if there really is something on my network exposing me.
BR,
Steve
@SteveDC It checks on what IP subnets the server runs, then checks from what client IP you are coming, and if your client IP isn't from one of the private networks or one of the server's configured ones it triggers that warnings. See here. You can disable that check via config.yaml by setting server.ipCheck.enabled to false. You can also add additional trusted subnets via server.ipCheck.trustedSubnets (list of subnets in CIDR notation).
I stumbled over this article and thought I'll give it a try... To be honest, some suggestions in it are really long shots.While offering some - in some cases, questionable - security, they limit the functionality greatly.
Let me step-by-step them:
-
Polarcloud: these guys have ridiculous requirements. Seriously, when trying to signup (with a google account), they forcibly requested access to "See, edit, create, and delete all of your Google Drive files" etc. I tried to research why this is needed, but the explanation was basically "we need it because we need it". This is a bad start already - however, I wanted to give it a shot and created a fresh Google account for this... Disappointed by the interface. Yes, you can upload and start the jobs, but it is cumbersome and does not give you much control.
-
Octoprint anywhere... The getanywhere page was down when I first read this article, so I returned later to it and signed up... The setup is easy, but the functionality is very limited. You can see the camera view and the temperature, and you can control some movement. That is. Did not even find a way to start a print job, let alone upload files etc.
-
Discord and Telegram... I do use telegram for notifications, but chat-based plugins are also very limited in their functionality. So while easy to setup, they do not offer what I need (YMMV, obviously).
Also, with both PolarCloud and OctoPrint anywhere you trust the vendor with your machine. You have no control whatsoever about which commands are really sent to the machine, you have to take the vendors word for it. Of course, you also have to take the vendors' word for the security of their environment - a blackhat controlling their servers would be able to send commands to your machine, too.
With this said, "advanced access" is from my opinion the only way to go. VPN is a good way to go, as well as reverse proxy - both allow you full control over your OctoPrint instance in a more or less safe way.
Getting an extra RasPI to be the endpoint for VPN or to run the reverse proxy will not cost you a fortune anymore (and some home routers have this functionality already off shelf), and the setup is no rocket science anymore either.
I've heard that port forwarding is bad, but PiVPN uses port forwarding. Does that mean that, the port that is forwarded is protected by the VPN? I am very new to networking, but I would like to get a CR10 and Octoprint instance running with full capabilities from a remote location.
I don't see many competing solutions paying for a third-party security audit. So the OpenVPN part of this will likely be shown to be secure.
PiVPN appears to have features where you specifically permission clients.
I WILL note that following the breadcrumbs of documentation and blog entries on their website did prompt me with what was likely a fake Flash Upgrade alert—so be careful.
Okay, thank you for the reply. I just commented in reply to you on another post about VPNs thinking that maybe I commented on the wrong thread. Fake Flash Upgrade alert? I'll have to look up what that means exactly. Thank you for the info!
It's like when you go to a website and there's a popup that suggests that:
- your Flash Player needs updating, click HERE
- your computer is at risk! click HERE
- we've scanned your computer and see that you have a virus, CLICK HERE
...etc. It's never a good idea to install anything when you visit a website.
Can the RPi used for the Octoprint install also be used for the VPN endpoint? Or do I need the two to be seperate?
In the lifetime of your printer, you'll likely have moments where you need to start over from scratch and re-flash your microSD with a new OctoPi.
I really wouldn't complicate matters by dropping the PiVPN on there as well. A Raspberry Pi Zero W is $5, you can get a 4GB microSD card for almost nothing these days, the power adapter is another $5 and a case for it is another $5 = $19 plus tax plus shipping. It's a small price to pay for the remote access you get in return.
And it's not just for your printer, you can remote into your desktop computers and servers, whatever.
Maybe it helps someone to make a first few steps into basic auth using the already installed haproxy on Octopi. I know this is not the most secure way, but I know 2 things: every installation out there that was at least secured a little bit is less risk, and most users won't use VPNs but cloud solutions instead, probably. Since clouds are insecure by design, I guess using the available haproxy and some basic user auth is a big step forward. Also, you can use every standard browser, there is no need for using any additional software or service. A small manual
https://wp.peters-webcorner.de/2019/01/how-to-secure-your-octoprint-installation/
How about using something like TeamViewer to access the home computer?
You likely can, but... You know, depending on the firmware, your PI could have lots of load already, so I wouldn't recommend it. Get a Pi Zero W and a power supply, and print a case for it.
I'd say this is kinda overkill. You need to have your home computer running, being waste of energy and an additional potential risk (yes, every electrical device operating while you are not at home is a risk). Plus, I tried to operate a TV-controlled PC through my iPhone. Once. Will never do it again. Never ever.
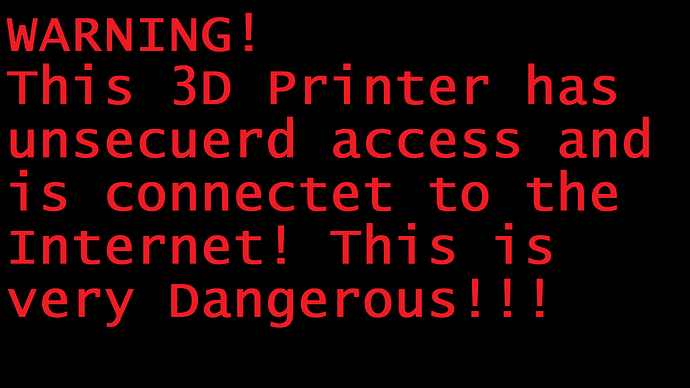
if you just type octoprint in the search of shodan.io, you sadly get a bunch of secured but often unsecured octoprint istaces for anyone to mess around with!!
Sou should cange the title to a warning and make a pic like tis one as the webcam stream, to help em
Honestly, I think foosel's done a good-enough job of first telling them what not to do and then upping the stakes by including a warning on their interface. She's created at least one thread on the subject, talked about it in video blog posts and has spent a fair amount of time educating people.
And here within the forum we do everything we can to convince people how to correctly setup their printers for safety.